It’s the end of the iPhone era for me.
I had been pretty impressed with the US iPhones that had leaked into NZ, and I bought an iPhone 3G on the first day they were available in NZ (using my own money even!) and upgraded it to a 3GS soon after that came out.
And it was great. Apple really were the first people to get the smartphone right. It was fast, had a useful screen and the touch interface had Apple’s usual attention to detail. My iPhone and I had a lot of good times together.
But by the time the iPhone 4 was released I just wasn’t as interested. It wasn’t just the hardware, or Apple’s control-freakery or any one thing in particular, but somehow I wanted to try something else.
What did happen was a Samsung Galaxy S II running Google’s Android operating system. I’ll be writing more about that later, but first I thought I’d finally get around to publishing my list of iPhone gripes.
These are my personal gripes. I know that some of them are probably features to other people, or can be fixed with more or less ease, or will be fixed in iOS5 but it’s really too late for that for me. So, in no particular order, a bunch of things that annoyed me about the iPhone:
- The failure to use the lock screen to display useful information.
- The way the weather app icon doesn’t change to match to match the weather.
- That the Maps icon is an American highway map.
- The difficulty of finding good apps – you can find a multitude of apps but it’s very hard to tell which are any good.
- The “icons, icons, nothing but icons” menu system.
- That the iPhone 3GS had very limited message notification and ringtones. You hear that “ding-ding” sound and every iPhone user in the room wonders if the message is for them.
- The way that iOS4.2 added new message tones for the iPhone 4 but not for the older 3GS.
- The lack of buttons, particular the way that the single button is used for search, task-switching, app-closing, and screen shots (about 10% of my photos are accidental screen shots),
- The lack of a physical camera button. Trying to do tricky shots wth the on-screen button is hard.
- The multi-second delay in starting the camera.
- The way that Apple offered free iPhone tracking… for the iPhone 4 but not the 3G or 3GS.
- The volume and mute controls on the 3GS have annoyingly sharp edges – and the mute button is too easy to activate when putting it into a pocket.
- There’s no icon on screen to show whether mute is on or not.
- That the iOS4 ‘upgrade’ killed the performance of the iPhone 3G and 3GS and Apple tried to stop you downgrading again. (This was improved in later versions but the performance is still noticeably crappier than it was.)
- The way that the 3G doesn’t get security fixes any more after just two years. (Launched July 2008, last fix Nov 2010).
- Apple choosing what political views are acceptable in apps sold in the app store – and there’s no other way to get apps.
- The inability to cache downloaded maps on your phone.
- The rotation-lock option cunningly hidden in a leftward swipe of the dock-thing when in task-switching mode.
- That you have to install iTunes to activate the phone or copy music to it.
- If you switch to a new PC, iTunes tries to get you to wipe everything from your phone (this can be prevented).
- That you can’t use the volume controls for page turning when reading electronic books.
- Lack of easy auto update for applications.
- If you’re in one application and click a link that takes you into another (e.g. a YouTube video link in the browser), there’s no obvious way to get back to where you were in the first application.
Coming soon: my list of Android gripes. :)
I feel remarkably disturbed by the release of the report from the Welfare Working Group.
Given that:
- The Domestic Purposes Benefit is designed to be the minimum necessary amount for people to live on.
- Currently it increases as additional children are born to cover the increased costs of food, clothing and so on.
- The WWG will substantially increase the pressure to get into work earlier.
- Failure to comply leads to a cut of the benefit paid in steps down to 0.
- These children, whether born to ‘good’ or ‘bad’ parents, still need to be cared for.
Let me be very clear about this – if your policies lead to children starving in a relatively rich country like New Zealand, you’re not just wrong or heartless, but evil.
One final note: some of the people who will be on the Domestic Purposes Benefit by the time these policies are implemented will only be so because they lost their partner in the Christchurch Quake.
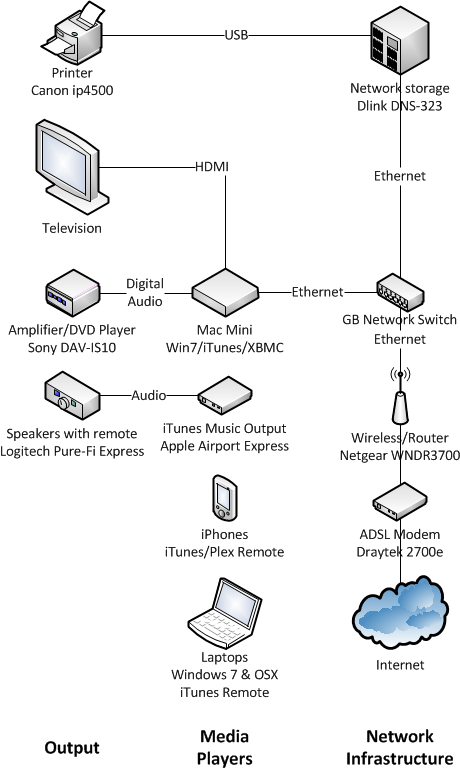
Three and a half years ago I documented my home entertainment system. I thought that people both technical and non-technical might appreciate the chance to see how someone else had done it.
It’s time for an update. Let’s start with what we can do with it:
Features
- Lounge – we use XBMC on the Mac Mini to play music, downloaded media and streaming Internet video. The all-in-one DVD player/amplifier is still used to watch movies on DVD.
- Bedroom – we use an Airport Express to play music from the network storage via iTunes running on the Mac Mini in the lounge. Our iPhones are used as remote controls. (Yes, there are a lot of systems involved in that process. Amazing that it works so well!)
- General – centralised storage of data, printing from anywhere, wireless Internet.
The Diagram
And here’s all the bits and how they connect up. As you can see it’s organised into three columns – output devices, players and network infrastructure:
Major Changes
The major changes since the last update:
- Dumped the old Xbox hardware for a media player and replaced it with an only slightly broken surplus Mac Mini running Windows 7. It’s still running XBMC. (Plex on OSX was rejected due to being a bit too unfinished – and I ended up hating the Apple Remote for not having enough buttons.)
- Upgraded the wireless network to dual-band 802.11n and the wired network to gigabit ethernet for maximum performance.
- Upgraded the network storage from 2 x 500Gb drives to 2 x 1.5TB drives, while still using the same old Dlink DNS-323 hardware.
- Switched to an ADSL internet connection due to not being able to get cable any more. We ended up having to run PPPoE from the ADSL modem to the router to make the connection stable enough to use.
- Added iTunes on the Mac Mini to enable use of an Airport Express as a remote music player.
- Added a Logitech Harmony remote (not shown) to control it all. This has allowed us to dump the other three remotes into a drawer and ignore them.
- Added an Xbox 360 (not shown) for gaming.
Next
It’s all working pretty well at the moment so no major changes are planned. The only limitation is that the Mac Mini isn’t powerful enough to play high-quality 1080p video. This could be solved by upgrading the hardware or by replacing it with a dedicated media player – if they ever get good enough (keeping my eye on the Boxee Box and the WD Live Hub). It doesn’t worry me too much at the moment.
Questions?
Feel free to ask any questions and I’ll do my best to answer them.
I was taken aback by what I found in my post box today – a letter asking me to complete a survey about my respiratory health. The Medical Research Institute tells me that (link to scan of letter (PDF)):
You have been randomly selected from the electoral roll to participate in the first phase which involves completing the questionnaire on the other side of this letter.
Personally I thought that it was illegal to use the Electoral Roll for any purpose other than elections, but it seems that there is an exception for approved scientific/health researchers.
I’d be surprised if the response rate was very high or very representative.
And no, I didn’t fill it out. Feel free to use the code and URL on the letter to go and answer it for me.
I was looking at the just released consultation document on Regulations and Codes of Practice for the Anti-Money Laundering/Countering the Funding of Terrorism Act.
They ask for submissions and add the following:
The Ministry of Justice does not intend to publish comment that it receives on this document. However any comment will be subject to the Official Information Act 1982 and may, therefore, be released in part or full.
This makes me feel like requesting all the submissions and publishing them (as Tech Liberty did for the ACTA submissions) just on general principle. Maybe if we keep doing that they’ll finally realise that it just makes more sense to publish the submissions themselves.
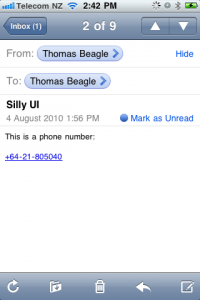
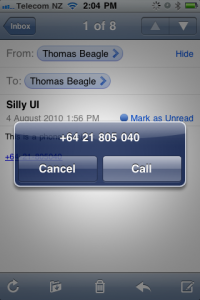
I really like the way that the iPhone recognises phone numbers in emails and turns them into touchable links.
But for ages I thought that all you could do was call the number.
This used to really annoy me because, being a modern kind of person, I generally prefer to text people than call them. Other times I just wanted the number to add to my address book, so I’d end up cutting and pasting the number into Contacts.
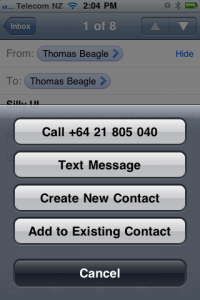
Then one day I lingered on the link too long and a whole new menu popped up! Hey, here were exactly the features I was looking for.
Now, there are two problems here.
Firstly, there is no advantage to the user from this arrangement. In both cases the phone displays a menu with one or more actions and an option to cancel it. The required user actions are the same:
- Press (or press and hold)
- Press selected option or cancel
If the user interaction is exactly the same why not just show the full menu in both cases?
Secondly, and more importantly, this “press and hold” functionality is hidden from the user and there’s no way to easily discover it. I’d had my phone for a couple of years before I realised it was there (I’m assuming it wasn’t added in an OS upgrade) and I wonder how many people still don’t know about it. And what other convenient features am I missing just because I haven’t thought to check that they might be there?
To my mind, “press and hold” is a user-unfriendly way to add functionality and should be avoided wherever possible.
Last week I went to my first Select Committee hearing and therefore I’m now an expert. Here’s what I found out.
Why
The New Zealand Council for Civil Liberties sent in a submission about the Electoral (Disqualification of Convicted Prisoners) Amendment Bill to the Law and Order Select Comittee.
Current law says that prisoners given a sentence of longer than 3 years cannot vote; this bill extends that to all prisoners. The Council opposes this change and recommends that this provision should be removed from the law, not extended.
In our submission we asked to make an oral submission to the committee.
Subsequently we received an invitation to appear before them. We were allocated 10 minutes to make our submission. Kevin was to do the submission while I went to support him.
Where
We turned up at Parliament 20 minutes before our time and went through the main visitor entrance. The receptionist asked us our business, gave us a sticker and then pointed us in the direction of the hearing rooms. The door was closed and a sign said that it was closed to the public. We sat down and chatted to the other submitters.
How
Eventually (they were late) the committee finished what they were doing, a whole bunch of people in suits filed out, and the sign on the door was changed to show that it was open to the public. We all filed in and sat in the public seats at one end of the room.
At the other end was a large U-shaped table with the various MPs around it, each with a computer terminal and a sign with their name in front of them.
What
The proceedings of the committee were fairly relaxed. The chair of the committee invited us up, quickly did introductions around the table and then asked us to speak.
Kevin gave his presentation and then the committee asked questions. The questions were generally quite good and showed that the committee members had listened to what he was saying – although some were obviously using our submission as a launch pad to put forward their own points of view. One committee member even asked for a copy of the statistics we had included in the presentation and then raced off to take copies.
Then the questions stopped and it was time for the next submitter to make their presentation, so we made our way out.
Acknowledgements
Thanks to Kevin McCormack of the NZ Council for Civil Liberties who wrote the original submission and then prepared and presented the oral submission.
Companies are increasing their use of Twitter but it’s not always obvious what they should be doing on it.
It doesn’t help that different people have different opinions. I’m not interested in following companies to get deals or beg for favours, and I detest “retweet to win” contests that try to turn everyone into unpaid spammers.
Here’s five times that companies made a positive impression on me by interacting over Twitter:
- Welcomed Whittakers (@whittakersnz) to Twitter and asked when they were going to do Easter Eggs. Got told they were working on it.
- Orcon offered to help me resolve a problem with their service. (Not solvable by them, it needed Telecom to pull finger.)
- I complained about Netgear service and got a phone call (!) from their PR company in Australia. I declined their offer to help and sorted it out through the usual channels the next day.
- Responded to a question about where to get batteries by suggesting Dick Smith. Someone else responded and speculated that their house-brand batteries might not be as good. @DickSmithNZ responded with details of their current sale on batteries as well as a link to a report showing that their batteries were as good as the name-brand ones.
- I said I was switching from Vodafone to Telecom and received a “Welcome on board” from @TelecomNZ.
Each of these companies treated me as a person and, by doing so, made me feel better about dealing with them.
The winner is Dick Smith for their quick and useful response – but I admit I’m still hanging out for those easter eggs from Whittakers!
Just having a look at the Summary Offences Act to see if it was illegal to be drunk in public (apparently it’s not) and found these:
Defence for public urination
Every person is liable to a fine not exceeding $200 who urinates or defecates in any public place other than a public lavatory. It is a defence in a prosecution under this section if the defendant proves that he had reasonable grounds for believing that he would not be observed.
Rewards
Every person is liable to a fine not exceeding $200 who Publicly advertises a reward for the return of any property that has been stolen or lost, and in the advertisement uses any words to the effect that no questions will be asked;
Postering
Every person is liable to a fine not exceeding $200 who, without the consent of the owner or occupier affixes any placard, banner, poster, or other material bearing any writing or pictorial representation to any structure, or to or from any tree;
Disturbing people
Every person is liable to a fine not exceeding $200 who, in any public place, unreasonably disrupts any meeting, congregation, or audience.
Peeping only happens at night
Every person is liable to a fine not exceeding $500 who is found by night without reasonable excuse peeping or peering into a dwellinghouse;
A friend asked me a set of simple questions: “Why are they doing this whole thing with the ACTA treaty? Why is it secret? Why is NZ participating?” He then followed up with: “Why are you against it?”
This set me thinking. There’s been lot of articles complaining about the secrecy around the ACTA negotiations (I’ve even written some) and worrying about the contents of it, but they often assume a certain level of knowledge of the base assumptions.
This article is an attempt to spell out some of the basic assumptions behind the opposition to the ACTA treaty. It’s a combination of some of the things I suspect are true, along with some of the claims I’ve seen from other people. As such it’s not a statement of how things are, but more a statement of what I and others fear to be true.
Some points that could be grouped to form an argument
- That the ACTA treaty is currently being negotiated by a number of countries including the USA, the EU, Australia and New Zealand.
- That the negotiation and the proposed content of the treaty is being kept a secret.
- That there is no plausible justification for negotiating the treaty in secret.
- That the ACTA treaty is going to go beyond anti-counterfeiting and try to impose new conditions around the use of copyright material.
- That compliance with the ACTA treaty will require signatories to implement domestic laws which specify draconian new penalties for people who breach copyright.
- That such penalties have long been a goal of those in the major content industries.
- That the content industry contributes a lot of money to US politicians.
- That US politicians are largely beholden to the people who financially support them.
- That the USA is behind the attempt to extend ACTA to copyright.
- That the USA knows that the wider public has a better understanding of copyright issues than the average politician.
- That the USA is behind the attempts to keep the ACTA negotiations secret as they know it will not stand up to mass scrutiny.
- That being a signatory of ACTA will be a pre-requisite to signing a free trade agreement with the US.
- That politicians in many countries, including New Zealand, see signing a free trade agreement with the US as good both for the country and their careers.
- That politicians don’t really understand the issues around copyright in the digital age.
- That politicians will be happy to sacrifice copyright issues if it gets them closer to a free trade agreement.